Microsoft 365 Security
Technical and administrative support to protect your devices, data, apps, and identities from cyber-attacks and other threats.
Microsoft 365 (as a SaaS provider) among others ensures the protection and availability of network, hardware, virtual environment, storage, operating system and system applications.
Microsoft 365 (as a SaaS provider) among others ensures the protection and availability of network, hardware, virtual environment, storage, operating system and system applications.
Updated on: 2023-10-19
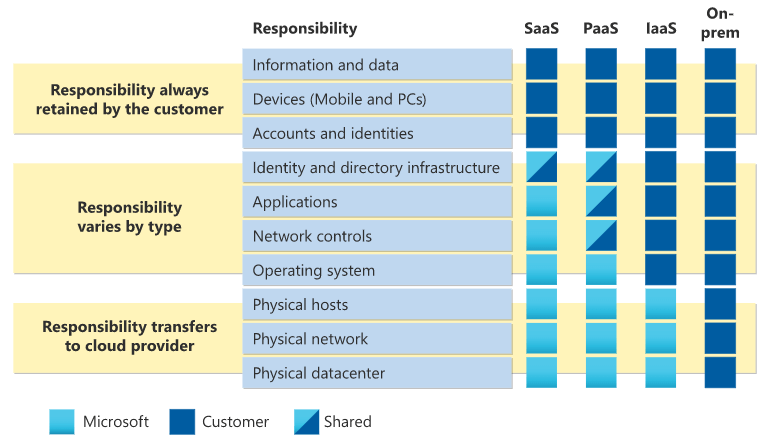
Responsibilities for SaaS products
Compared to the on-premises network where the hardware and software are hosted internally, Microsoft 365 as a SaaS solution is hosted and managed by the provider.There are many other differences between on-premise and SaaS solutions. It is worth mentioning that despite many tasks that the provider takes over, SaaS solution is about 40-60% cheaper in terms of cost-effectiveness. In the case of nonprofit organizations, even more advantageous.
Customer (if needed together with us) takes care of:
- Own data and information with backup, access rights, data protection
- Device management (PCs, notebooks, smartphones) with data encryption, software updates, virus protection
- User account management and protection through password length and complexity requirements, MFA, logon from trusted sites etc.
In addition to user, group and data permissions, these are the most important tasks that are the responsibility of the customer: Authentication, endpoint security, encryption, and data backup, which we discuss below.
Source: docs.microsoft.com
Authentication
Regardless of the service you are accessing, especially in cloud services, a password length of at least 12 characters consisting of upper case letters, lower case letters, numbers and symbols is essential.How often the password is changed can be considered as secondary. In certain security environments and for administrators, password changes should be enforced by policy. It is very important that different passwords are used with different providers.
The proven multi-factor authentication (MFA) should always be implemented. This means that users must perform two or more independent authentication methods when logging in. Common methods are verification codes on another device, via SMS or app.
Device security
Another important element of cloud security is the protection of devices or endpoints. Usually users access cloud services via web browsers, so client-side security, especially keeping the browser up to date, is very important.Implementing an endpoint security solution such as Microsoft Intune and Microsoft Microsoft Defender for Endpoint to protect your endpoints in the cloud environment is even more important. This solution includes features such as firewall, antivirus, apps protection, intrusion detection etc.
Investing in Endpoint security is especially important for home office work, as the employer has no control over the network layer. When working inside the office it is also recommended, because only then the protection on the network level can be seen as a second priority.
Unfortunately, it can be assumed that over time the increase of threats will be greater and greater.
Encryption
Data encryption during transmission via HTTPS has been a standard for a while now. This is the case for data access via browser at the cloud provider as it is the case for Office 365 apps.Encryption of data at rest as in the case of hard disk encryption for mobile devices must be ensured.
Encryption of mobile devices is very important to prevent unauthorized access to corporate data, as in the case of loss. This task can also be managed centrally through Microsoft Intune.
Own encryption solutions can also be considered for data that resides in the cloud to maintain full control over your data.
Data backup
By default, Microsoft 365 does not include a classic backup solution. Nevertheless, there are the following ways to restore data:- Versioning, to restore Office documents to different previous versions
- When deleting user accounts, restore them with user data within 30 days
- Deleted data from SharePoint can be restored within 90 days
- Deleted emails from Exchange can be restored by an administrator within 14 days, or after 30 days if it has been previously set to do so
- Certain data may also be retained for several years if an appropriate retention policy has been set
There are numerous third party vendors that implement backup solutions, we can assist you with this.
Contact and Support
☏ +49 721 66980 610
Write to us,
you can expect an answer on the same or next working day.
you can expect an answer on the same or next working day.
Get together and talk
We would be happy for you to pick a time (right here) and arrange a free online meeting with us via Microsoft Teams. For example, we can discuss how you can optimise your M365 licenses and reduce costs.
Customer support
We are here to help you with any questions you may have about Microsoft 365 and Azure. You can count on our support at fair prices in the range of 70-90 EUR per hour. We can use your ticket system or our support Jira ServiceDesk, see sample ticket.
You will be supported by security experts who continuously update their Microsoft skills and prove them with manufacturer certificates. This is a MUST for us to keep customer support at the highest level and up to date with the latest technology.
 Copyright 2003 - 2024 Sylbek Cloud Support
Copyright 2003 - 2024 Sylbek Cloud SupportYour IP 3.145.130.31, your resolution , our time



